Generating Rsa Private Key From Pfx
It fails because code001.private only contains an RSA key, while pkcs12 expects a certificate to go with it. In addition, as said by Stephane, the -nokeys option will cause openssl to skip the private key. You can generate a certificate with. Openssl req -new -x509 -key code001.private -out code001.pem.
- What is the easiest way for a newbie to RSA to create & use a key pair on Windows? Ask Question. Add it to your windows personal certificate store (typically, just double-click on the PFX file that contains your certificate and private key). Help to understand secure connections and encryption using both private/public key in RSA?
- That changes the meaning of the command from that of exporting the public key to exporting the private key outside of its encrypted wrapper. Inspecting the output file, in this case privateunencrypted.pem clearly shows that the key is a RSA private key as it starts with -BEGIN RSA PRIVATE KEY-. Visually Inspect Your Key Files.
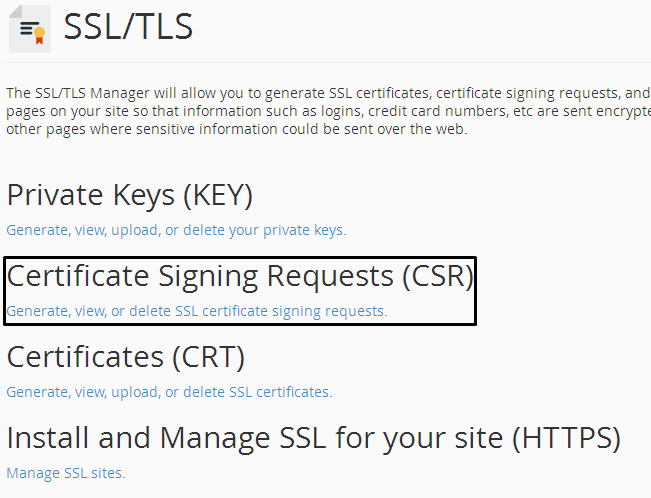
Set OPENSSLCONF=c:openssl-win32binopenssl.cfg openssl pkcs12 -in filename.pfx -nocerts -out key.pem openssl rsa -in key.pem -out myserver.key. The private key will be saved as ‘myserver.key’. Carefully protect the private key. Be sure to backup the private. Sep 11, 2018 The first thing to do would be to generate a 2048-bit RSA key pair locally. This pair will contain both your private and public key. You can use Java key tool or some other tool, but we will be working with OpenSSL. To generate a public and private key with a certificate signing request (CSR), run the following OpenSSL command. Set OPENSSLCONF=c: openssl-win32 bin openssl.cfg openssl pkcs12 -in filename.pfx -nocerts -out key.pem openssl rsa -in key.pem -out myserver.key. The private key will be saved as ‘myserver.key’. Carefully protect the private key. Be sure to backup the private key, as there is no means to recover it, should it be lost.
Generate RSA keys with SSH by using PuTTYgen
One effective way of securing SSH access to your cloud server is to usea public-private key pair. This means that a public key is placed onthe server and a private key is placed on your local workstation.Using a key pair makes it impossible for someone to log in by using justa password, as long as you set up SSH to deny password-basedauthentication.
This article provides steps for generating RSA keys by using PuTTYgen onWindows for secure SSH authentication with OpenSSH.
Generate keys
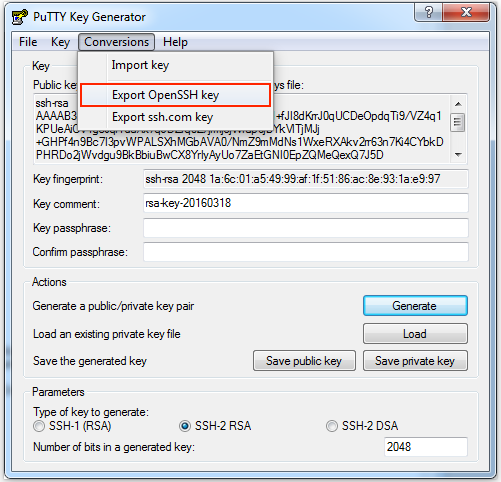
In Windows, use PuTTYgen to generate your public and private keys.
3 FreeIPA Training Series User authentication in sshd SSH supports multiple mechanisms for authenticating users Password authentication, public key authentication, GSSAPI authentication, Public key authentication uses digital signatures to verify the user's identity The user's private key is stored on the client (/.ssh/idrsa) The user's public keys are stored on the server. Adding your SSH key to the ssh-agent. Before adding a new SSH key to the ssh-agent to manage your keys, you should have checked for existing SSH keys and generated a new SSH key. When adding your SSH key to the agent, use the default macOS ssh-add command, and not an application installed by macports, homebrew, or some other external source. 3 FreeIPA Training Series Introduction to SSH public key management (2) Usually, public keys are stored in OpenSSH-style files Host public keys are in knownhosts files (global or per-user) User public keys are in authorizedkeys file (per- user) Public keys are managed by manipulating these files on each system Manually editing them by the administrator or user.  How to set up passwordless SSH access for root user duplicate Ask Question Asked 8 years ago. Active 1 year, 7 months ago. When you are prompted for a password, just hit the enter key and you will generate a key with no password. Next you need to transfer the key to the server. How To Set Up SSH With Public-Key Authentication On Debian Etch Preliminary Notes. This mini-howto explains how to set up an SSH server on Debian Etch with public-key authorization (and optionally with disabled password logins).
How to set up passwordless SSH access for root user duplicate Ask Question Asked 8 years ago. Active 1 year, 7 months ago. When you are prompted for a password, just hit the enter key and you will generate a key with no password. Next you need to transfer the key to the server. How To Set Up SSH With Public-Key Authentication On Debian Etch Preliminary Notes. This mini-howto explains how to set up an SSH server on Debian Etch with public-key authorization (and optionally with disabled password logins).
- If needed, download PuTTYgen from the PuTTY download page.(PuTTYgen might have been installed previously with PuTTY or WinSCP.)
- Launch the program, and then click the Generate button.The program generates the keys for you.
- Enter a unique key passphrase in the Key passphrase andConfirm passphrase fields.For additional information about using passphrases,see Log in with a SSH Private Key on Windows.
- Save the public and private keys by clicking the Save public keyand Save private key buttons.
- From the Public key for pasting into OpenSSH authorized_keys filefield at the top of the window, copy all the text (starting with ssh-rsa)to your clipboard by pressing Ctrl-C.You need this key available on your clipboard to paste eitherinto the public key tool in the Control Panel or directly into theauthorized keys on your cloud server.
Use the key pair
You can use the RSA key pair in the following ways.
Specify your SSH key when creating a new cloud server
When you create a cloud server, you can assign a public key from the list of keys.If your key is not already in the list, you may add it, and then assign it.
Add a new public key to the list
- Under Advanced Options on the Create Server page, click Manage SSHKeys.
- Select public key for the cloud server from the SSH Keys listand click Add Public Key.
- Enter the key name, select the region, and paste the entire publickey into the Public Key field. Then click Add Public Key.
- Go back to the Create Server page, and confirm that your key is listedin the SSH Key list.
Assign a public key
- Under Advanced Options on the Create Server page, select the publickey you want to use from the SSH key drop-down menu.
- When you are done specifying the all the other details for the server,click Create Server.
Assign your SSH Key to an existing cloud server
Create Cert And Key From Pfx
To make use of your newly generated RSA key pair, you must tell PuTTY touse it when connecting to your cloud server.
To edit the file (or create it), run the following command on the cloud server:
Paste the text onto its own line in the file.
You must have the key available in your clipboard to paste it. The key and itsassociated text (the ssh-rsa identified at the start and the comment at the end)must be on one line in the file. If the text is word-wrapped onto multiple linesan error might occur when connecting.
If you created the authorized_keys file, change its permissionsafter you’re done editing it by running the following command:
Open PuTTY, and go to the SSH > Auth section.
Browse to the location of the key file, and load the private key.
Go to the Session page, and save the session. This saves the configurationso that PuTTY uses the key every time that you connect to your cloudserver.
After you save your session, your key is loaded automatically when youconnect to your server.
Related article
Experience what Rackspace has to offer.
©2020 Rackspace US, Inc.
Openssl Export Private Key From Pfx
Except where otherwise noted, content on this site is licensed under a Creative Commons Attribution-NonCommercial-NoDerivs 3.0 Unported License